Fintech software powers everything from mobile payments to cryptocurrency exchanges, but building it requires more than standard development skills. You need to handle strict regulations, process high transaction volumes, and maintain security that protects user funds and data.
This guide covers what makes fintech different, the types of products you can build, and the technical decisions that determine whether your system scales or collapses under real-world pressure.
Key takeaways
- Fintech requires security-first development with encryption, multi-factor authentication, and role-based access controls from day one.
- Compliance requirements like PCI DSS, GDPR, and KYC/AML regulations shape architecture decisions and data handling practices.
- Microservices architecture with containerization enables independent scaling of critical components during peak transaction loads.
- Financial transactions must be atomic with rollback mechanisms, idempotency for duplicate requests, and complete audit logging for regulators.
What makes fintech software development different
Fintech software handles financial operations: payments, lending, trading, insurance, and wealth management. It goes beyond mobile banking apps to include the following:
- regtech – regulatory compliance tools
- insurtech – insurance platforms
- wealthtech – investment management systems
Unlike standard software development, fintech requires stricter security protocols and regulatory compliance from day one. A bug in a social media app might frustrate users. A bug in a payment system can result in financial losses, legal penalties, and damaged trust.
Types of financial products and solutions
Fintech covers a wide range of financial services, each with distinct technical requirements and regulatory constraints.
1. Payment systems and digital wallets
Payment systems process transactions between users, merchants, and banks, handling authorization, settlement, and reconciliation across multiple payment networks. Digital wallets store payment credentials securely and enable contactless payments through mobile devices or web browsers.
Example: Stripe provides payment infrastructure for online businesses, handling credit card processing, subscription billing, and international payments through a single API.
Building payment systems means achieving PCI DSS compliance, implementing real-time fraud detection, and integrating with card networks, banks, and alternative payment methods. Transaction failures, chargebacks, and currency conversions add complexity to what seems like simple money movement.
2. Mobile banking platforms
Mobile banking apps replace branch visits with account management, money transfers, bill payments, and mobile check deposits. These apps connect to core banking systems while delivering modern features like budgeting tools, spending analytics, and instant notifications that traditional banks struggle to match.
Example: Chime offers fee-free banking with early direct deposit and automatic savings features, operating entirely through mobile and web interfaces without physical branches.
Security requirements go beyond standard mobile apps. Bank-grade encryption, biometric authentication, and real-time synchronization with backend systems are baseline expectations. The fintech apps must function during network interruptions, manage sessions securely, and protect sensitive data stored on devices that users might lose or have stolen.
3. Credit systems
Credit platforms transform loan applications from multi-day processes into instant decisions. They assess borrower risk, process applications, and manage repayment schedules using machine learning models that analyze credit scores, income verification, transaction history, and alternative data sources that traditional lenders ignore.
Example: Affirm provides point-of-sale financing for online purchases, making instant credit decisions using machine learning models and integrating directly into merchant checkout flows.
Lending regulations like the Truth in Lending Act dictate disclosure requirements and fair lending practices. These platforms integrate with credit bureaus for risk assessment, bank accounts for income verification, and payment processors for collecting repayments. Collections processes must follow strict legal guidelines that vary by jurisdiction.
4. Trading platforms
Trading platforms execute buy and sell orders for stocks, bonds, cryptocurrencies, and other assets while providing real-time market data, order management, portfolio tracking, and risk analysis. Speed determines success – traders abandon platforms that lag behind market movements.
Example: Robinhood offers commission-free stock trading through a mobile-first interface, processing millions of trades daily with real-time price updates.
Connections to exchanges, clearinghouses, and market data providers must handle millions of orders during volatile trading sessions. Order routing algorithms seek the best execution prices across multiple venues.
Partial fills, cancelled orders, and market volatility create edge cases that require careful handling. Regulatory compliance demands complete audit trails showing when orders were placed, modified, and executed.
5. Blockchain and cryptocurrency solutions
Blockchain platforms enable decentralized transactions, smart contracts, and digital asset management without banks or payment processors as intermediaries. Distributed ledger technology records transactions across multiple nodes, creating transparent and immutable records that no single party controls.
Example: Coinbase provides cryptocurrency exchange services, supporting dozens of cryptocurrencies with custody, security, and regulatory compliance across multiple jurisdictions.
Cryptographic security protects user funds, but private key management creates usability challenges – users who lose their keys lose their assets permanently. Network congestion during high demand periods increases transaction fees and processing times.
Cryptocurrency regulations evolve rapidly, with different jurisdictions taking conflicting approaches to taxation, licensing, and consumer protection.
Not sure where to start with your project?
Get free advice from developers with 25+ years of experience.
We’ll get back to you within 1 business day to suggest possible next steps.
Security requirements for fintech systems
Security shapes every technical decision in financial software development. A single breach destroys user trust, triggers regulatory penalties, and ends your business.
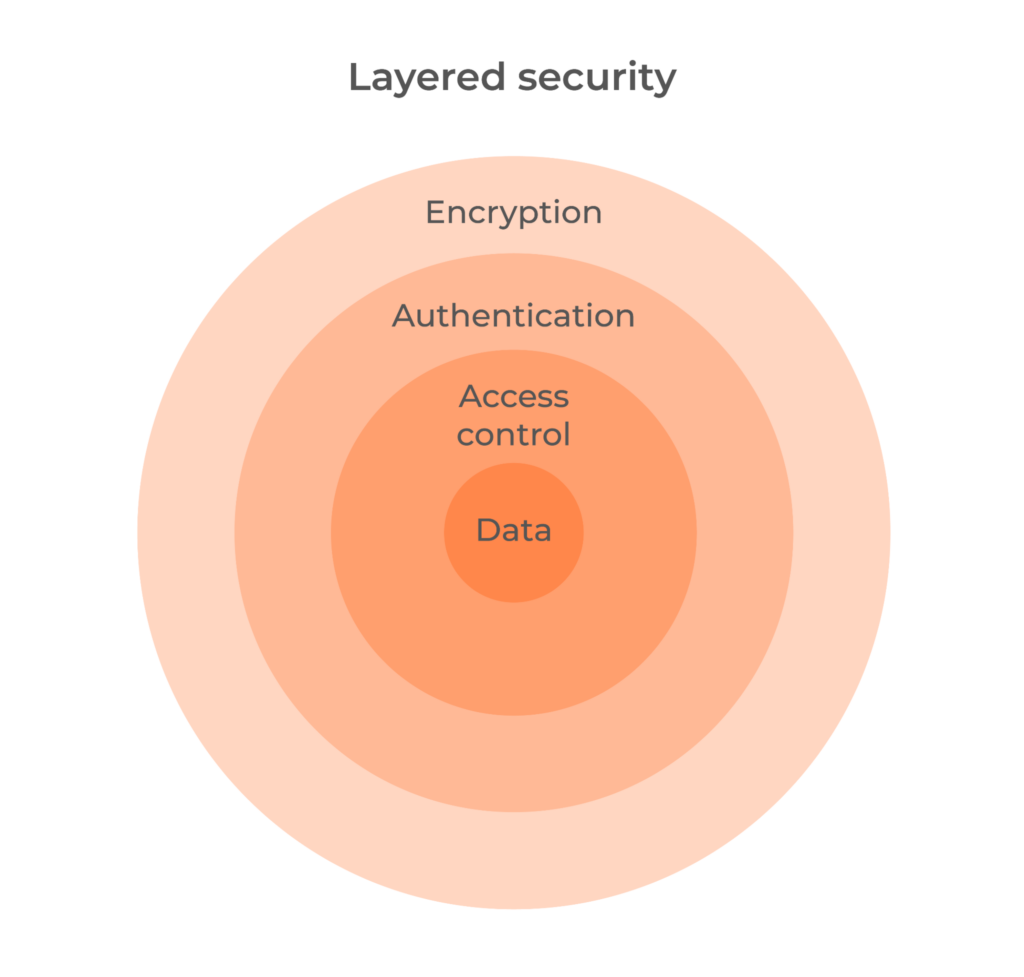
Encryption and secure communication
All data must be encrypted in transit and at rest. TLS 1.3 or higher protects communication between clients and servers, preventing attackers from intercepting account credentials, transaction details, or personal data during transmission. This applies to user-facing applications, microservice communication, and third-party API integrations.
Sensitive data storage requires strong encryption algorithms like AES-256 for database fields containing financial information, social security numbers, and authentication credentials. Encryption keys must be managed separately from encrypted data using dedicated key management services.
Passwords need specialized hashing algorithms like bcrypt or Argon2 that include salt and computational complexity, making brute-force attacks impractical even if attackers obtain your database.
Identity and access management
Multi-factor authentication combines something the user knows (password), something they have (phone or hardware token), and optionally something they are (biometric data). This layered approach prevents unauthorized access even when passwords are compromised through phishing or data breaches.
Role-based access control limits what users and services can do within your system. A customer service representative needs different permissions than a financial analyst or system administrator.
The principle of least privilege means granting only the minimum access required for each role. Session management requires cryptographically random tokens, appropriate expiration times, and detection of suspicious login patterns like multiple failed attempts or concurrent sessions from different geographic regions.
Secure API design
APIs expose your system to external clients and third-party services, making them common attack vectors. Authentication through OAuth 2.0 or API keys verifies every request, while input validation and sanitization prevent injection attacks. Rate limiting protects against abuse and denial-of-service attacks by setting request limits based on user tier and endpoint sensitivity.
API versioning manages changes without breaking existing integrations. A public endpoint for checking account balances might allow 100 requests per minute, while money transfer endpoints require stricter limits. Monitoring API usage reveals anomalies like unusual request volumes, repeated failed authentication attempts, or suspicious data access patterns that indicate potential attacks.
Security monitoring and incident response
Continuous monitoring detects security threats through logging of authentication attempts, financial transactions, and API access. Security information and event management (SIEM) systems analyze logs for suspicious patterns like multiple failed logins, large transactions, or unusual access patterns.
An incident response plan defines roles, communication protocols, and escalation procedures before breaches occur. When security incidents happen, teams must contain the threat, assess damage, notify affected users and regulators, and implement fixes. Preparation through tabletop exercises reduces response time and limits damage during actual security events.
Compliance and regulatory frameworks
Different fintech products face different regulatory requirements. Compliance affects architecture decisions, data handling practices, and operational procedures.
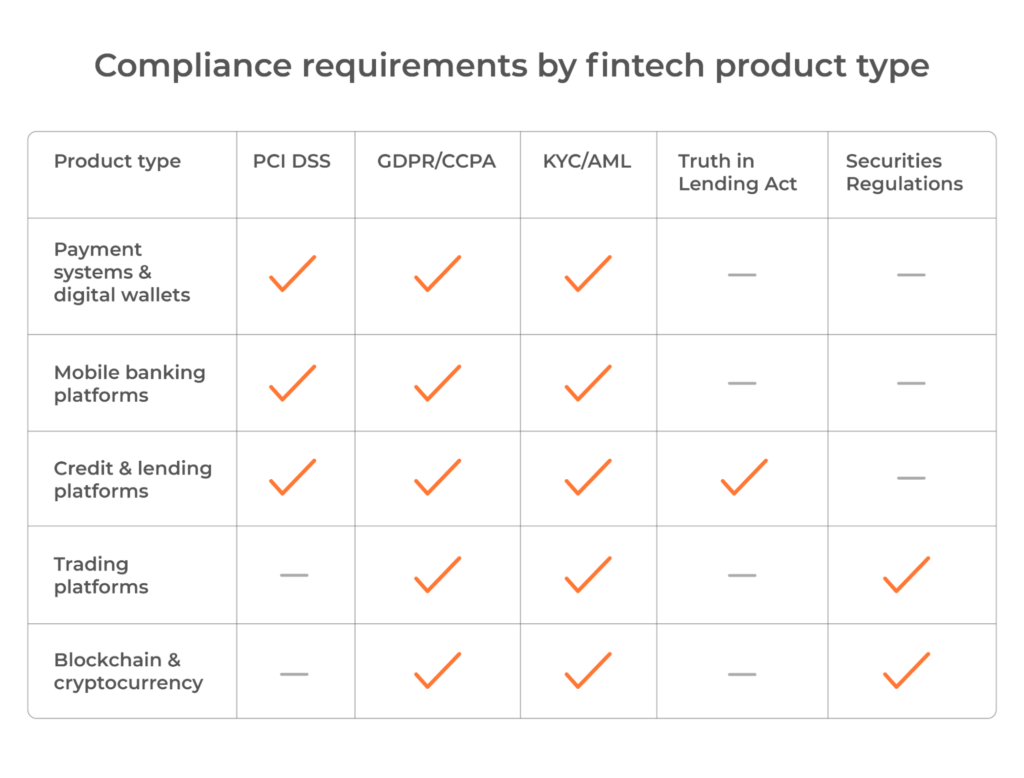
Payment processing compliance
Payment processors must comply with PCI DSS for handling credit card data. This standard requires network segmentation, regular security testing, access controls, and encryption of cardholder data. Compliance validation occurs annually through self-assessment questionnaires or third-party audits depending on transaction volume.
Data protection regulations
GDPR applies to services handling European user data, requiring explicit consent, data deletion rights, and breach notification within 72 hours. CCPA provides similar protections for California residents. These regulations mandate transparent data collection practices, user access to their data, and the ability to request deletion.
Financial services regulations
Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations require identity verification and transaction monitoring for services that move money or provide financial accounts. The Bank Secrecy Act mandates reporting of suspicious activities and large transactions. Lending platforms must comply with the Truth in Lending Act for disclosure requirements and fair lending practices.
Ongoing compliance requirements
Compliance isn’t a one-time certification but an ongoing process. Audit logging must track every system action for regulatory reviews, creating immutable records of who did what and when. Regular security audits verify controls remain effective. Documentation of data flows, security controls, and incident response procedures supports regulatory examinations.
How to build fintech software
Building fintech software requires a structured approach that balances speed with regulatory requirements. Each phase addresses specific technical and compliance challenges that can derail projects if ignored early.
1. Research the market
Start by identifying your target users and understanding their specific pain points with existing financial services. Study competitors to understand what works in the market and where gaps exist.
This research goes beyond feature comparison – you need to understand transaction volumes, peak usage patterns, and performance expectations that will shape your technical architecture.
Talk directly to potential users about their current solutions and frustrations. A payment app for small businesses faces different challenges than a high-frequency trading platform. Small business owners might prioritize simple invoicing and fast settlements, while traders need millisecond-level execution speeds and advanced charting tools.
2. Decide on architecture and tech stack
Your architecture and technology choices determine how your system handles transactions, scales under load, and meets regulatory requirements. Fintech applications typically use microservices architecture, which separates critical functions like payment processing, user authentication, and transaction logging into independent services that communicate through APIs.
Selecting your tech stack involves choosing components across multiple layers of your system:
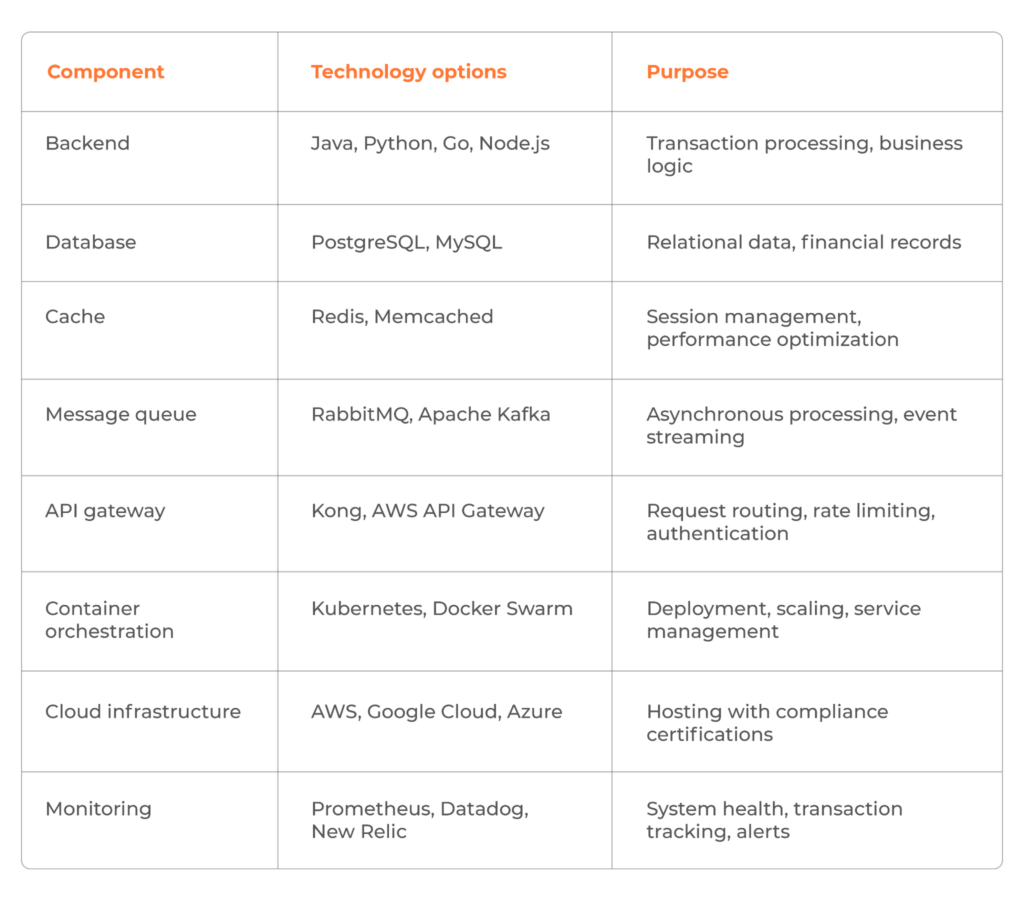
Plan for operational requirements that can’t be retrofitted easily once the system is running. Data encryption protects information both at rest in databases and during transmission between services. Automated backups and disaster recovery procedures ensure you can restore operations after hardware failures, security incidents, or data corruption.
3. Get to design and development
Design user interfaces that simplify complex financial operations without hiding important information. Users need clear confirmation of transaction amounts, fees, and recipients before they commit.
Build authentication and authorization systems first – these form the foundation for all other features. Implement multi-factor authentication, session management, and role-based access controls early in development.
Transaction processing requires careful error handling and rollback mechanisms. Financial operations must be atomic: either the entire transaction completes successfully, or it rolls back completely.
Partial transactions create reconciliation problems and compliance issues. Implement idempotency to handle duplicate requests safely – if a user clicks “pay” twice due to network delays, the system should process the payment only once.
Use version control, code reviews, and automated testing throughout development. Every code change should go through peer review to catch security vulnerabilities and logic errors. Write unit tests for business logic, integration tests for API endpoints, and end-to-end tests for critical user flows.
Document API endpoints, data flows, and security controls for compliance audits. Build admin dashboards for monitoring transactions, user activity, and system health.
4. Do QA, testing and compliance checks
Test transaction accuracy under various scenarios: successful payments, failed payments, partial refunds, and currency conversions. Run load testing to verify the system handles expected transaction volumes during peak hours. Simulate network failures, database outages, and third-party API downtime to ensure graceful degradation.
Verify compliance with relevant regulations before launch. This includes reviewing data handling practices, consent mechanisms, audit logging, and incident response procedures.
Prepare documentation for regulatory submissions and certifications. Some regulations require formal audits or certifications before you can process real transactions. Factor these timelines into your launch schedule – compliance reviews can take weeks or months depending on the jurisdiction and product type.
Performance and scalability architecture
Fintech systems must handle growing user bases, transaction volumes, and regulatory requirements without performance degradation. Here are some finance software development tips that will help you scale efficiently without expensive rewrites later.
1. Microservices and containerization
Microservices architecture isolates critical functions like payment processing, user authentication, and transaction logging into separate services. This isolation simplifies updates, improves fault tolerance, and makes it easier to scale specific components under heavy load.
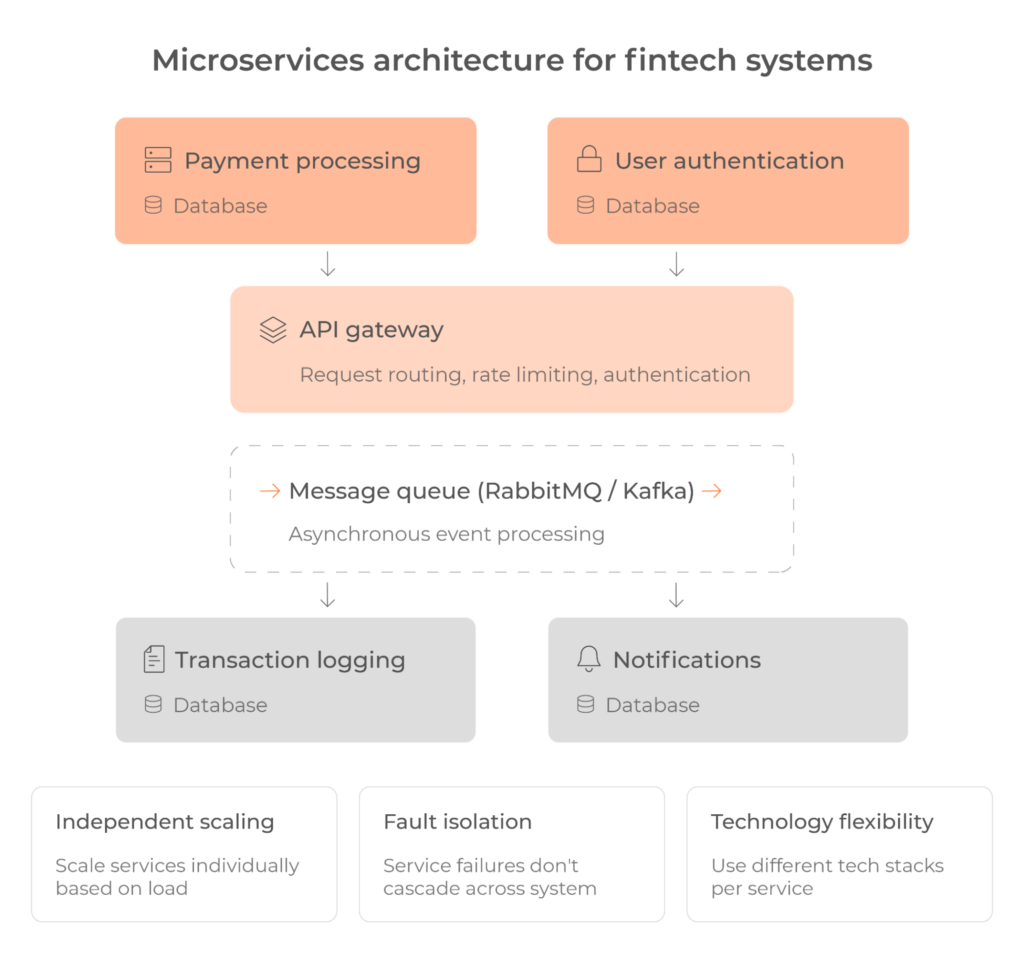
Containerization with Docker packages each service with its dependencies, ensuring consistent behavior across development, testing, and production environments. Kubernetes orchestrates these containers, automatically scaling services based on load, restarting failed instances, and distributing traffic across healthy nodes.
When payment processing experiences high load during peak hours, Kubernetes scales only that service while other components run at normal capacity. This targeted scaling reduces infrastructure costs.
2. Event-driven architecture
Event-driven architecture uses message queues to handle asynchronous operations. When a user initiates a payment, the system publishes an event to a queue. Separate services consume these events to process the payment, send notifications, and record audit logs. This approach decouples services and prevents cascading failures.
Event-driven systems handle traffic spikes gracefully. If notification services fall behind during high load, messages queue up without blocking payment processing.
3. Database scaling strategies
High-transaction systems require horizontal scaling: adding more servers rather than upgrading existing ones. Design stateless services that store sessions in Redis or distributed caches so any server can handle any request.
Use read replicas to distribute database query load across multiple instances. Implement sharding to partition data across servers by geographic region or account ID ranges. Each shard handles a subset of transactions, reducing load on individual databases.
Cache frequently accessed data like account balances or exchange rates to reduce database queries. Set appropriate cache expiration times to balance performance with data freshness. Monitor query performance and add indexes for frequently queried fields.
4. Low latency requirements for trading platforms
Trading platforms require sub-millisecond response times for order execution. Latency directly affects trading outcomes – delays of even a few milliseconds result in missed opportunities or unfavorable prices.
Server location matters significantly for trading systems. Deploying servers in close physical proximity to exchange data centers through colocation reduces network latency by minimizing the distance data travels. Direct market access connections eliminate intermediaries that add processing delays.
Code optimization becomes critical at this performance level. Compiled languages like C++ or Rust outperform interpreted languages in performance-critical components. In-memory data stores handle market data and order books because disk I/O introduces unacceptable delays. Binary serialization protocols like FIX transmit data more efficiently than text-based formats like JSON, reducing both processing time and bandwidth usage.
Latency monitoring requires precision measurement at every system layer. Network round-trip time, application processing time, and database query time all contribute to total latency. Percentile-based metrics reveal more than averages – the 99th percentile latency matters more than the median because consistent performance determines trading success.
Conclusion
Building fintech software requires balancing technical complexity, regulatory compliance, and security from the start. Success depends on choosing the right architecture, understanding your target market’s regulations, and planning for scale before you need it.
Fintech development demands specialized expertise across multiple domains: software engineering, financial systems, security, and compliance.
If you need experienced developers who understand these challenges, contact Setronica. We build fintech solutions that meet regulatory requirements without compromising performance or user experience.
Chapters
- Key takeaways
- What makes fintech software development different
- Types of financial products and solutions
- Security requirements for fintech systems
- Compliance and regulatory frameworks
- Performance and scalability architecture
- Conclusion



